Prerequisites
This section outlines the prerequisites for deploying SambaStack and guides you through obtaining the necessary credentials and configurations.SambaNova collects hardware prerequisites (such as load balancer configuration) and OS configuration requirements (such as NTP servers) through the SambaNova site survey. Contact your SambaNova representative for details.
- This guide assumes you have a kubernetes cluster already in place.
- You must provide two TLS certificates and DNS names for the API and UI endpoints:
api.<your-domain>— certificate and private keyui.<your-domain>— certificate and private key
- You must provide certificates as either:
- Two individual certificates (one for each hostname), or
- A single wildcard certificate (e.g.,
*.example.com) covering both
Self-signed certificates are not supported for production environmentsCertificates must be issued by a trusted Certificate Authority (CA) such as Let’s Encrypt, DigiCert, or your organization’s internal CA - Ensure the following tools are installed/present:
- Helm
- kubectl
- Google Cloud CLI (gcloud) | Requirement | Specification | | :— | :— | | Kubernetes version | v1.30+ (recommended) | | Helm version | v3.19+ (recommended) | | Control planes | Core Services Rack (CSR) includes 3 control planes for SambaStack | | Data planes | SambaRack worker nodes serve as data planes |
- Make sure you have received the following from SambaNova
- Helm chart OCI registry URLs
Chart Registry URL SambaStack Base oci://<REGISTRY_URL>/sambastack/sambastack-baseSambaStack oci://<REGISTRY_URL>/sambastack/sambastackSambaNova provides the full registry URL,service-account-keyfile, and version number during handover. Contact your SambaNova representative for access credentials.Version numbers change with new chart releases. Check with your SambaNova representative for the current installation version. - Configuration files
- Sample
sambastack.yamlfile for your deployment - this guide also shows how to build this from scratch.
- Sample
- Google Cloud service account key file. This file is used to create:
- Image Pull Secret
- Artifact reader secret
- Helm chart OCI registry URLs
Setup
Authenticate and Configure Cluster
- Create sambastack namespace
- Create a Docker registry secret for pulling images from Artifact Registry using your Google Cloud service account JSON key:
- Create a secret for reading model artifacts from Google Cloud Storage:
- Label each RDU node for scheduling. Add
--overwritefor idempotency:Repeat this command for each node in your cluster.
Configure `sambastack.yaml`
- Configure a minimum viable
sambastack.yamlfile:This default file deploys a bundle that you will be able to query by including entries under thebundles.bundleSpecsandbundles.bundleDeploymentSpecssections.SambaRack SN40L-16 systems may have either 12TB or 4TB of DDR memory, but all newly shipped systems are 4TB, so configure the cluster memory limit accordingly and use the lower limit when mixing node types.See the SambaStack.yaml Reference for a full example.
Helm Login and Install
- Use your Google Cloud service account to authenticate with the Helm registry:
- Install the base chart and main SambaStack chart:
SambaNova provides the full registry URL and version number during handover. Contact your SambaNova representative for access credentials.
Version numbers change with new chart releases. Use the version number provided by your SambaNova representative.
Refer to the Pods reference table for details on the pods created after installation.
Ensure Pods are Running
- Run the following command to see all the pods running in your cluster:
- Make sure all pods are
Running. Your response should resemble the following:It usually takes about 5-10 minutes for all the pods to reach their desiredRunningstate.See the Pods reference table for more details.
Create User and API Key
This quickstart guide uses the default keycloak auth setup to get started. To configure custom authentication, check out the authentication page.
- Retrieve keycloak
temp-admincredentials: - Port forward keycloak
- Log into keycloak at
http://localhost:8080/withtemp-admincredentials above.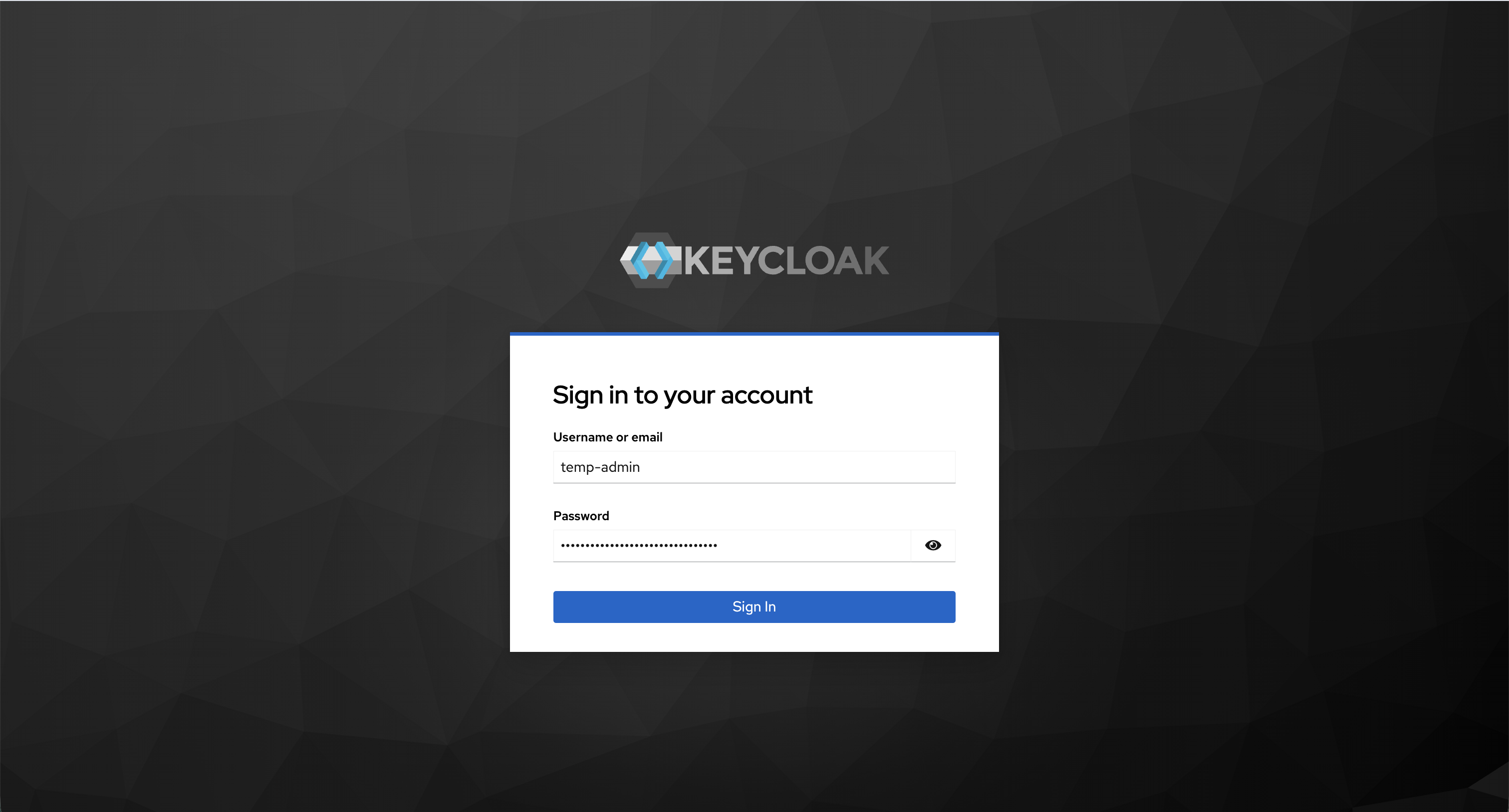
- Create admin user
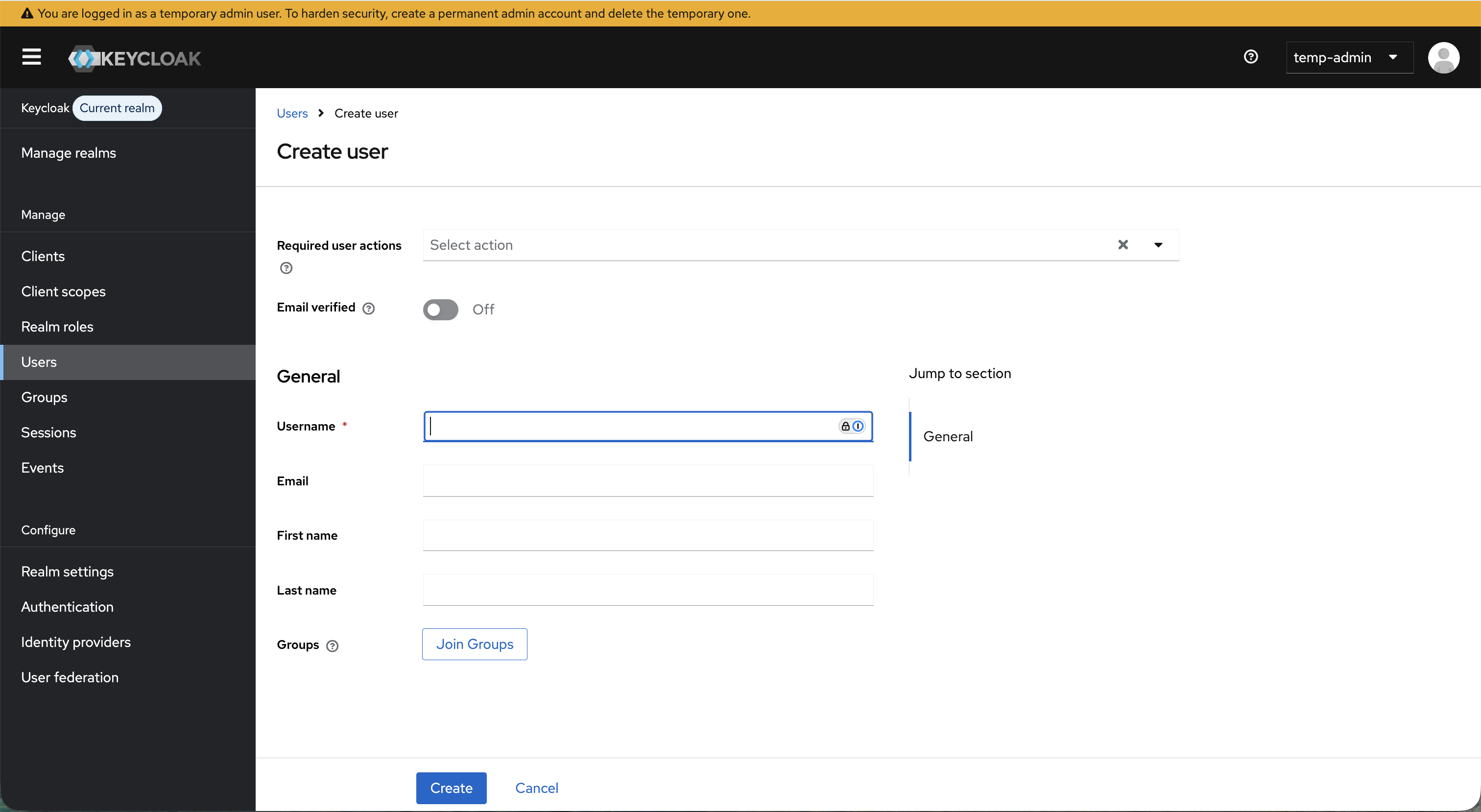
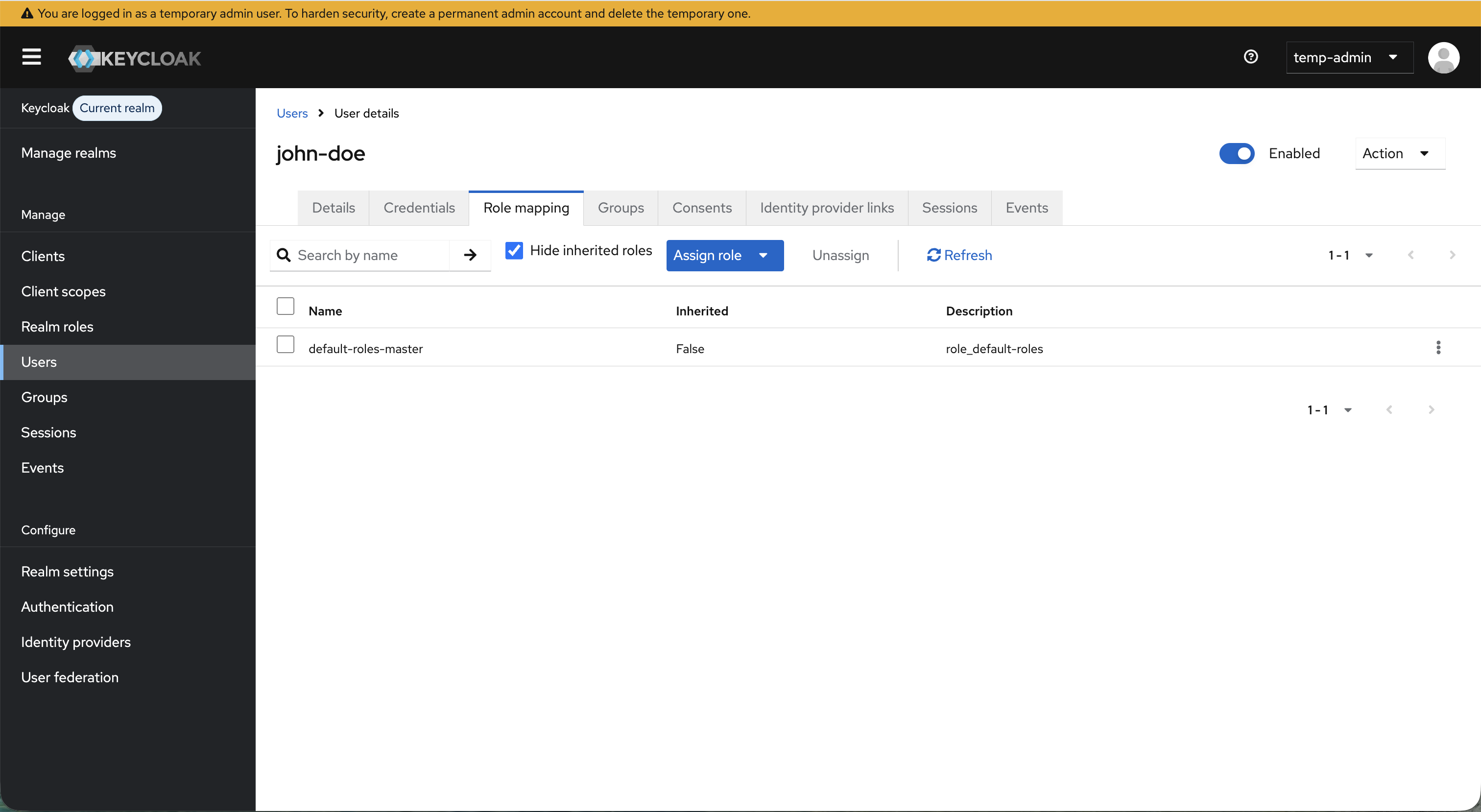
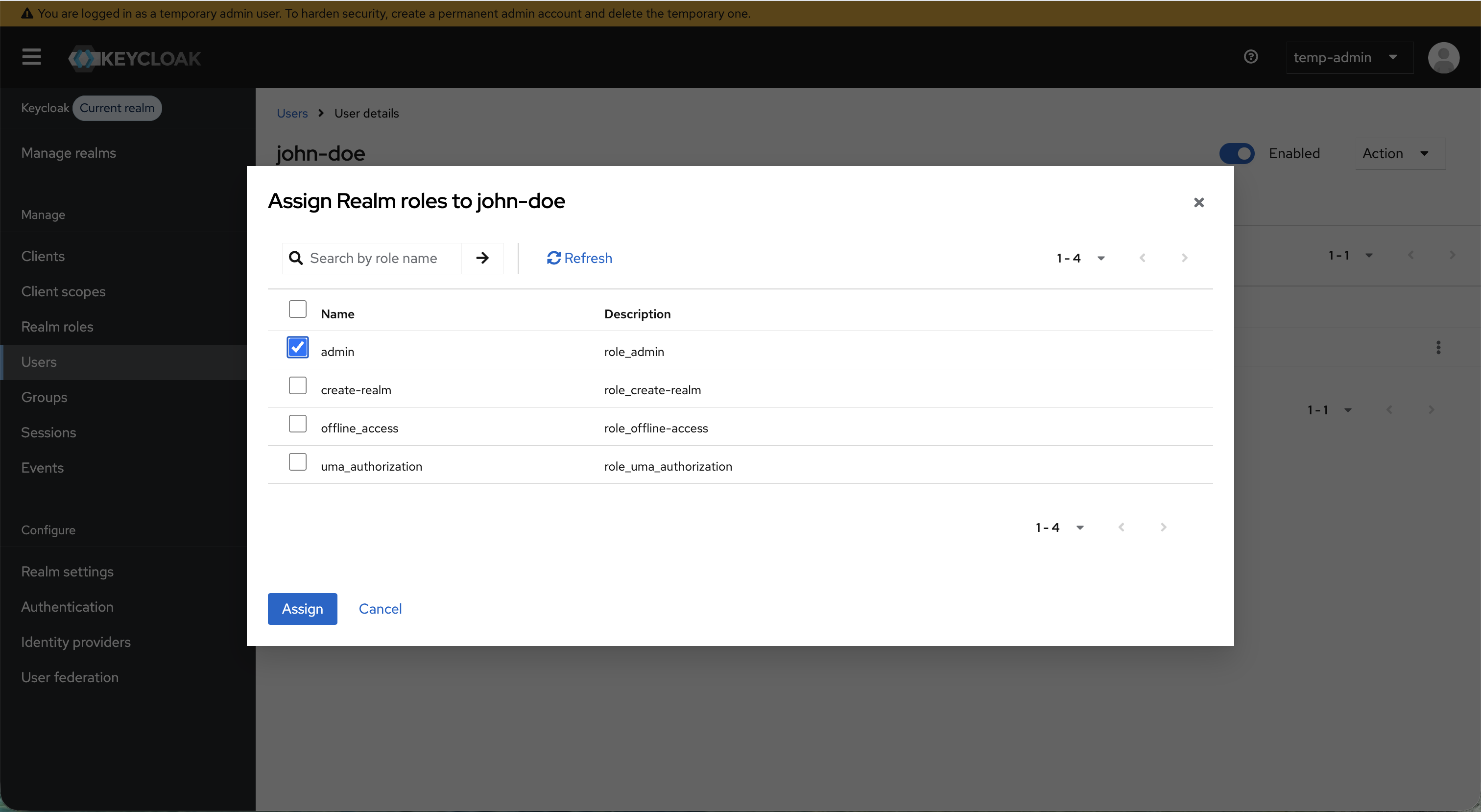
- Assign admin role
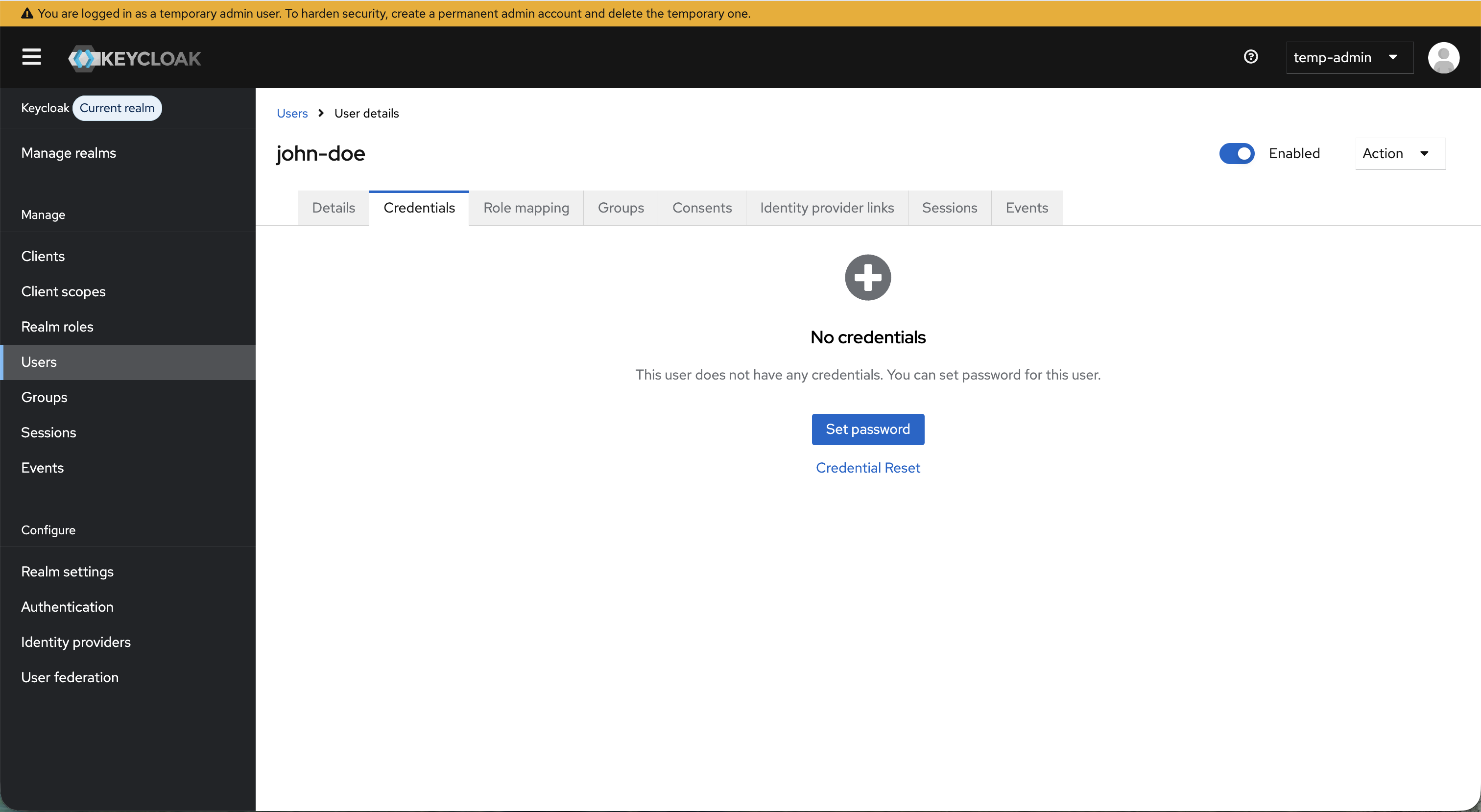
- Set admin credentials
- Add admin user email to the
db-adminsection ofsambastack.yaml:See the SambaStack.yaml Reference for a full example. - Visit
ui.<your-domain>and log in with user credentials retrieved above.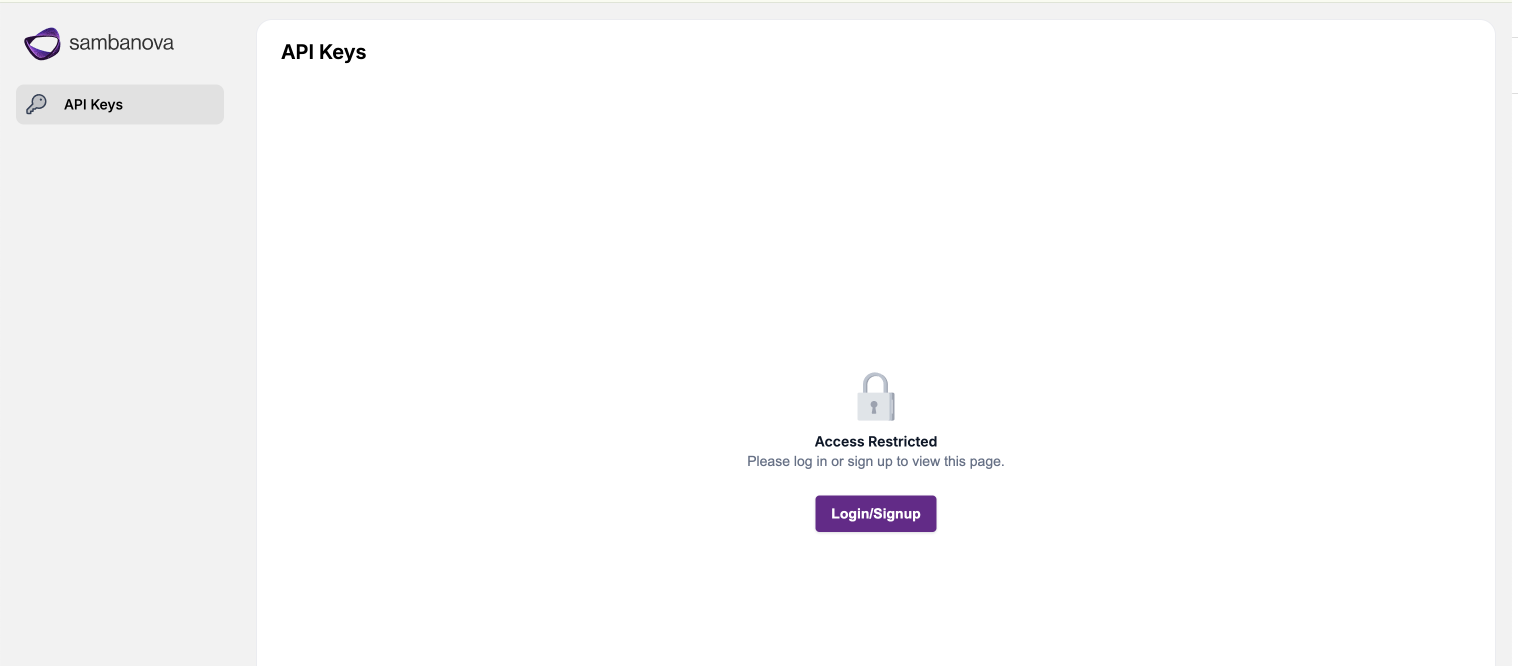
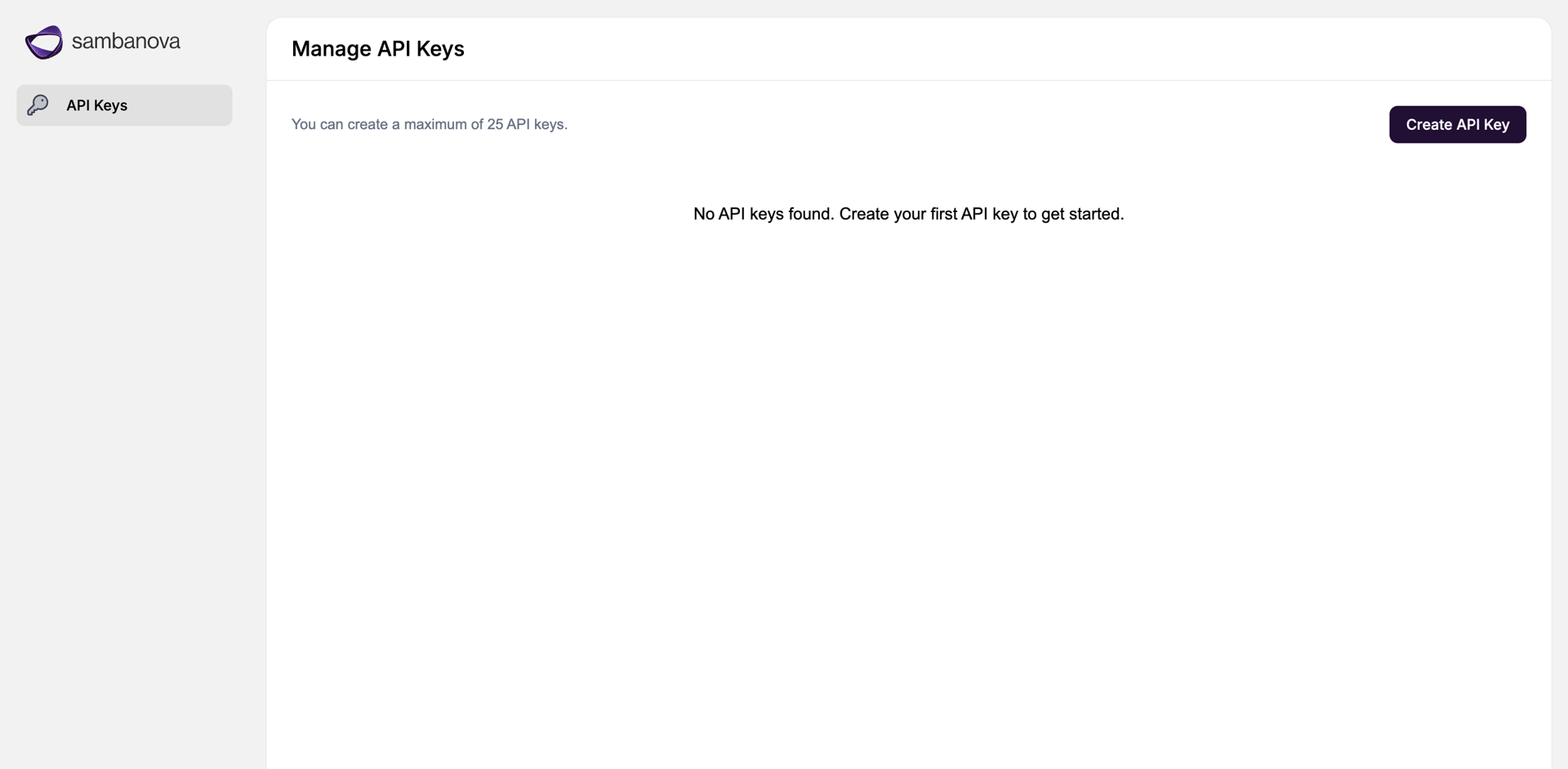
- Create API key and save securely: